 |
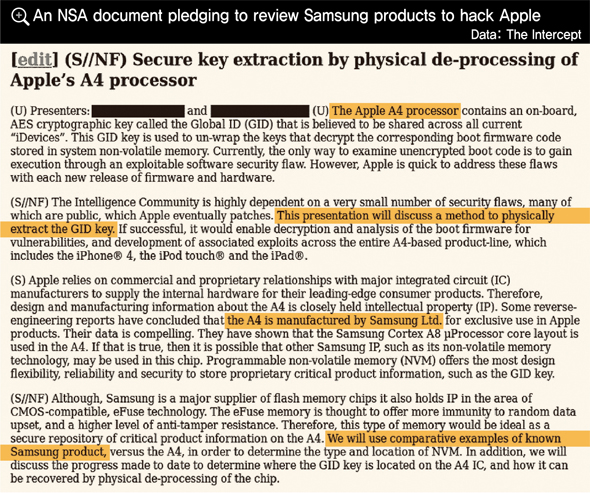
An NSA document pledging to review Samsung products to hack Apple, Data: The Intercept |
Relationship can be described as a paradox, where cooperation is more about the US’s own interests
In an interview with German weekly Der Spiegel, Thomas Drake, a former employee for the US’s National Security Agency (NSA), described the NSA’s relationship with Germany by saying, “It’s a sort of paradox in that relationship.”Drake was drawing attention to the fact that, while Germany and the NSA are partners, the NSA does not hesitate to spy on Germany when the US’s national interest is on the line.The concept of a paradoxical relationship also applies exactly to relations between South Korea and the NSA. The Hankyoreh became the first newspaper to report that the NSA analyzed a number of products by Samsung Electronics in an effort to develop hacking technology. Intelligence cooperation, but only when it coincides with US needsOfficially, the NSA has been maintaining a cooperative relationship with South Korea for quite some time. This cooperation began with the outbreak of the Korean War on June 25, 1950.One of the documents leaked by Snowden, titled “Official SIGINT Partners,” contains a list of countries that the NSA regards as allies. Australia, Canada, New Zealand, and the UK - the other members of the “Five Eyes” intelligence-sharing body - are part of tier two, which is closest to the US. Thirty-three countries, including South Korea, Japan, and Germany, are included in tier three. These countries are considered to be more loosely allied than the Five Eyes countries.It was the Snowden documents published by journalist Glenn Greenwald in May 2014 that confirmed for the first time that South Korea has been assisting the NSA with collecting SIGINT, or signals intelligence.A document titled “Paying Expenses to Partners in the 2012 Fiscal Year” shows that 15 countries earned money in connection with an NSA initiative called the Combined Cryptologic Program (CCP). A line graph indicates that South Korea was paid between US0,000 and US0,000.South Korea is on a similar level with Israel, while Pakistan received the most money, totaling US.5 million.There is no explanation about what the money was given in exchange for. Considering that “CCP,” the acronym for the Combined Cryptologic Program, appears in the document, it is assumed that these countries were helping the NSA with internet surveillance.These cooperative relationships bear the hallmarks of unrequited love. The US’s true motivations are laid bare in a document titled, “What Are We After with Our Third Party Relationships?” The document, which was one of the articles that appeared in the Sep. 2009 issue of a classified newsletter for US intelligence agents, consists of a newsletter staff member’s interview of an NSA deputy assistant for SIGINT operations who is responsible for cooperating with other countries.The NSA only formed cooperative relationships when the payout was clear.“If we can meet our objectives -- particularly short-term ones -- working through CIA, that’s okay. If, on the other hand, our SIGINT exchanges increase in volume and/or complexity, or if a direct partnership is necessary because . . . we need rapid, direct exchange of communication . . . we will establish a formal SIGINT relationship, after DNI approval,” the deputy assistant said. DNI refers to the Director of National Intelligence.The US, according to the deputy assistant, is compensated for these cooperative relationships with high-priority target communications, regional information, and foreign language capability.“We can only move our SIGINT relationships forward, when US requirements intersect with [the national interests of these third parties],” the deputy assistant said in answer to another question.The document also contains a clue about why NSA activity is not very well-known in South Korea.When the interviewer asked if “foreign intelligence relationships [are] usually insulated from short-term political ups and downs,” the deputy assistant said that political issues overseas “rarely disrupt” these intelligence relationships. “Few senior officials outside of their defense-intelligence apparatuses are witting to any SIGINT connection to the US/NSA,” the deputy assistant said.This effectively explains why, even when cooperation is taking place between the South Korean government or its intelligence agencies and the NSA, it is hard for high-ranking officials inside the government (aside from those who are directly involved with this cooperation or associated with those who are) to figure out what is really happening. Anyone can be spied on when the national interest is involvedOn the other hand, when it comes to the national interest of the US and other countries in Five Eyes, South Korea, just like any other country, can become the target of snooping. One well-known example was the South Korean UN delegation in New York was wiretapped.But there are other past examples that are not as well-known. In a book about the NSA, journalist and former US navy intelligence analyst James Bamford related how Canada‘s Communications Security Establishment created a surveillance system with technical help from the NSA. Canada is one of the members of the Five Eyes group.“In the 1990s, the Communications Security Establishment spied on the diplomatic posture of South Korea after several conferences with Canadian trade officials about the CANDU reactor, which was developed by Atomic Energy of Canada. Canada intercepted communications that were passing into and out of the South Korean Embassy in Canada,” Bamford wrote in his book.In the process of reviewing all of the Snowden documents, a document was discovered that contained a plan by the NSA to analyze Samsung parts in order to develop hacking technology.In an article titled, “Secure Key Extraction by Physical De-Processing of Apple’s A4 Processor,” the NSA said,“ The Intelligence Community is highly dependent on a very small number of security flaws, many of which are public, which Apple eventually patches. This presentation will discuss a method to physically extract the GID key.” The GID key refers to a security key used in Apple products.After mentioning the fact that the Samsung Cortex A8 microprocessor is used in the Apple A4 processor, the document says, “We [the NSA] will use comparative examples of known Samsung product, versus the A4, in order to determine the type and location of NVM [non-volatile memory].”The implication is that the NSA was planning to review a wide number of products by Samsung - which supplies parts for Apple - in order to hack Apple products. However, this document, which is only one page long, does not specify whether the NSA actually tested Samsung products or, if it did, what the results were.When a Hankyoreh reporter asked whether Samsung parts could be used to hack Apple products, Samsung Electronics responded that it could not comment about anything related to its clients.With the caveat that it was not responding to the document itself, the company said that there are various kinds of attacks that can be made against chipsets and that the kind mentioned in the Snowden documents also exists.“If you’ve prepared for an attack, it’s unlikely that you‘ll be hacked,” the company added. “When supplying semiconductors, we [Samsung Electronics] implement distinctive security technology in order to protect our clients and their intellectual property from various kinds of hacking.”Another Snowden document about spying on social media mentions the term “Cyworld.” The term appears alongside other social media services in a chart showing which social networks were popular in 2007. There is no explanation, however, about whether this is merely an informative graph or whether the NSA actually hacked Cyworld.By Kwon Oh-sung and Ko Na-mu, staff reportersPlease direct questions or comments to [english@hani.co.kr]
english.hani.co.kr/arti/english_edition/e_international/716965.html



